
As announced in the last report, i started looking into SSO solutions and evaluated and tested them. At the begining my focus was on SAML integration, but i soon realized that OAuth2 would be more important.
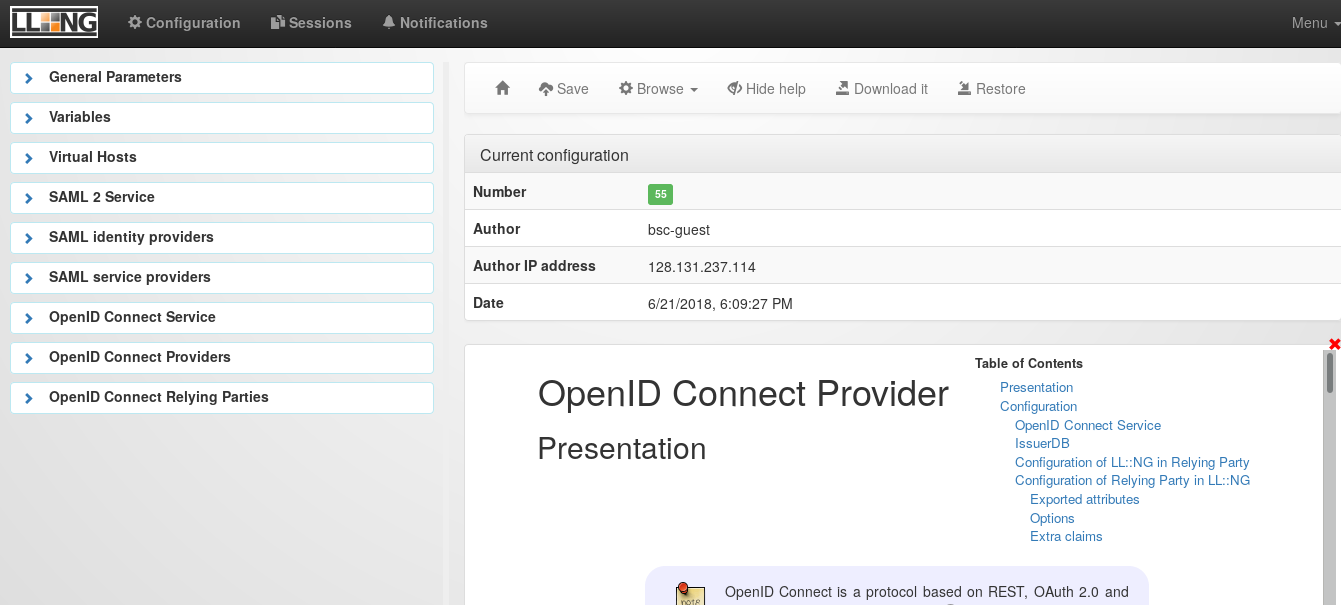
I started with installing Lemonldap-NG. LL-NG is a WebSSO solution writting in perl that uses ModPerl or FastCGI for delivering Webcontent. There is a Debian package in stable, so the installation was no problem at all. The configuration was a bit harder, as LL-NG has a complex architecture with different vhosts. But after some fiddling i managed to connect the installation to our test LDAP instance and was able to authenticate against the LL-NG portal. Then i started to research how to integrate an OAuth2 client. For the tests i had on the one hand a gitlab installation that i tried to connect to the OAuth2 providers using the omniauth-oauth2-generic strategy. To have a bit more fine grained control over the OAuth2 client configuration i also used the python requests-oauthlib module and modified the web app example from their documentation to my needs. After some fiddling and a bit of back and forth on the lemonldap-ng mailinglist i managed both test clients to authenticate against LL-NG.
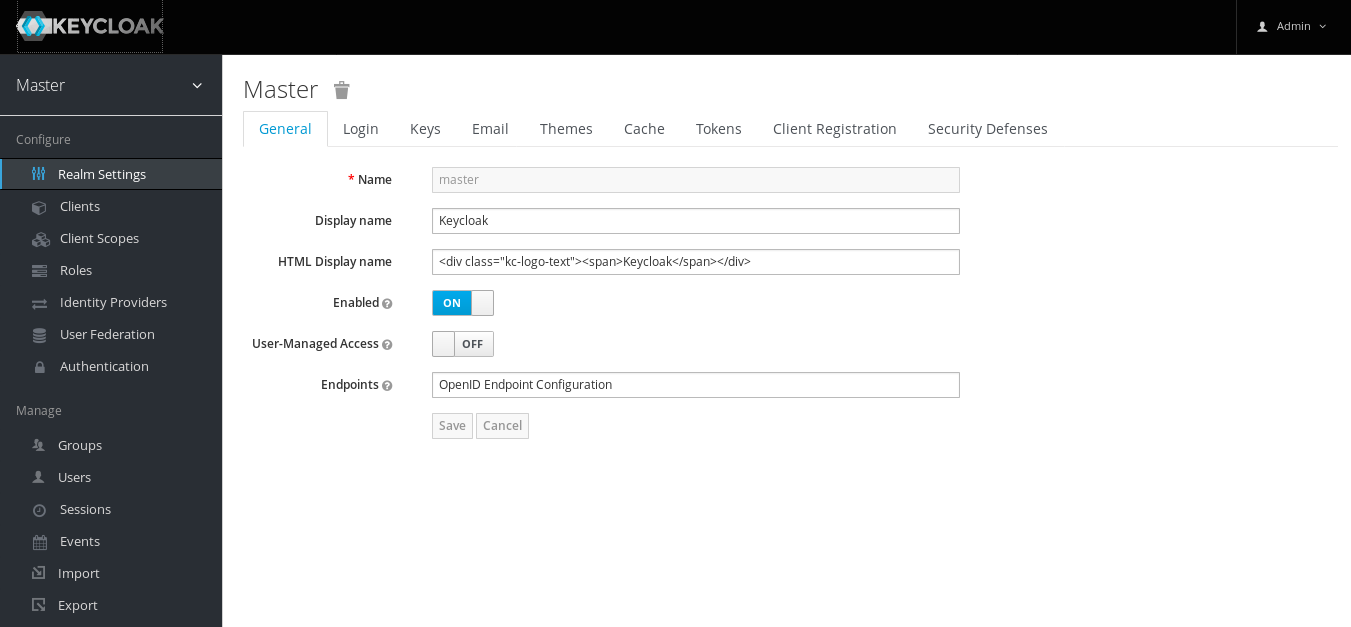
The second solution i tested was Keycloak, an
identity and access management solution written in java by Redhat. There is no
debian package, but nonetheless it was very easy to get it running. It is
enough to install jre-default from the package repositories and then run the
standalone script from the extracted keycloak folder. Because keycloak only
listens on localhost and i didn’t want to get into configuring the java
webserver stuff, i installed nginx and configured is as a proxy. In Keycloak
too the first step was to configure the LDAP backend. When i was able to
successfully login using my LDAP credentials, i looked into configuring an
OAuth2 client, which wasn’t that hard either.
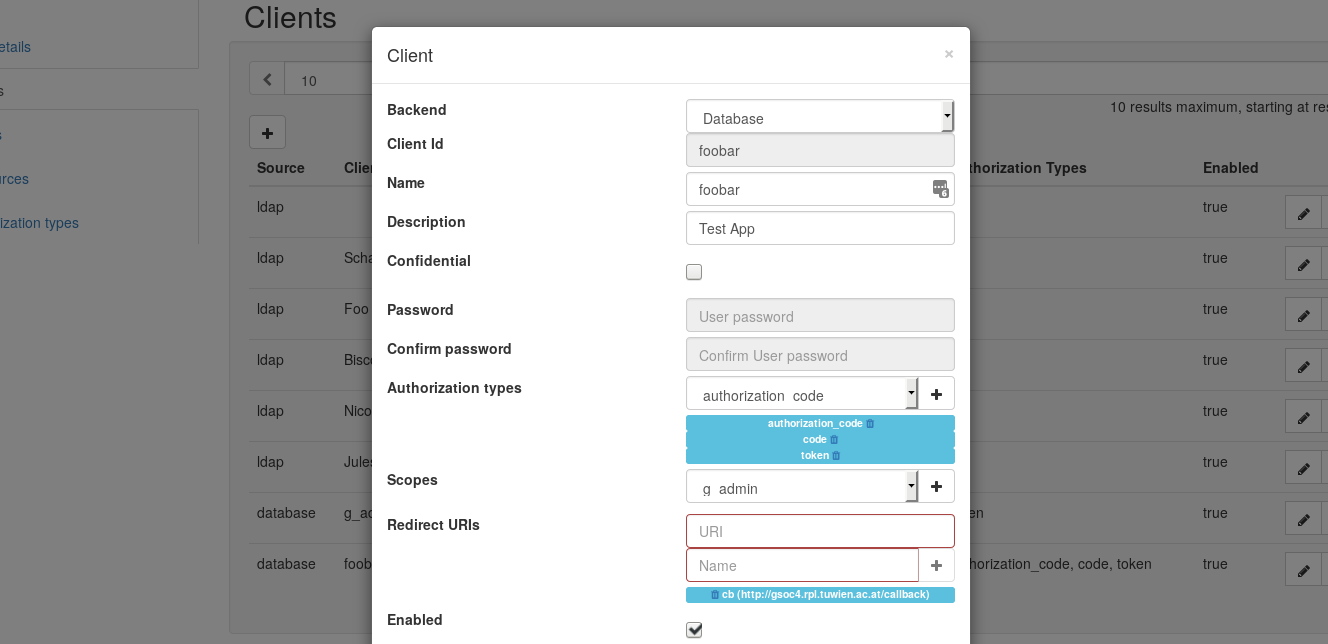
The third solution i looked into was
Glewlwyd, written by babelouest.
There is a Debian package in buster, so i added the buster sources, set up apt
pinning and installed the needed packages. Glewlwyd is a system service that
listens on localhost:4593, so i also used nginx in this case. The configuration
for the LDAP backend is done in the configuration file which is on Debian
/etc/glewlwyd/glewlwyd-debian.conf. Glewlwyd provides a webinterface for
managing users and clients and it is possible to store all the values in LDAP.
The next steps will be to test the last candidate, which is ipsilon and also
test all the solutions for some important features, like multiple backends and
exporting of configurable attributes. Last but not least i want to create a
table to have an overview of all the features and drawbacks of the solutions.
All the evaluations are public in a salsa
repository
I also carried on doing some work on nacho, though most of the issues that
have to be fixed are rather small. I reguarly stumble upon texts about Python
or Django, like for example the Django
NewbieMistakes and try to
read all of them and use that for improving on my work.
debian gsoc18